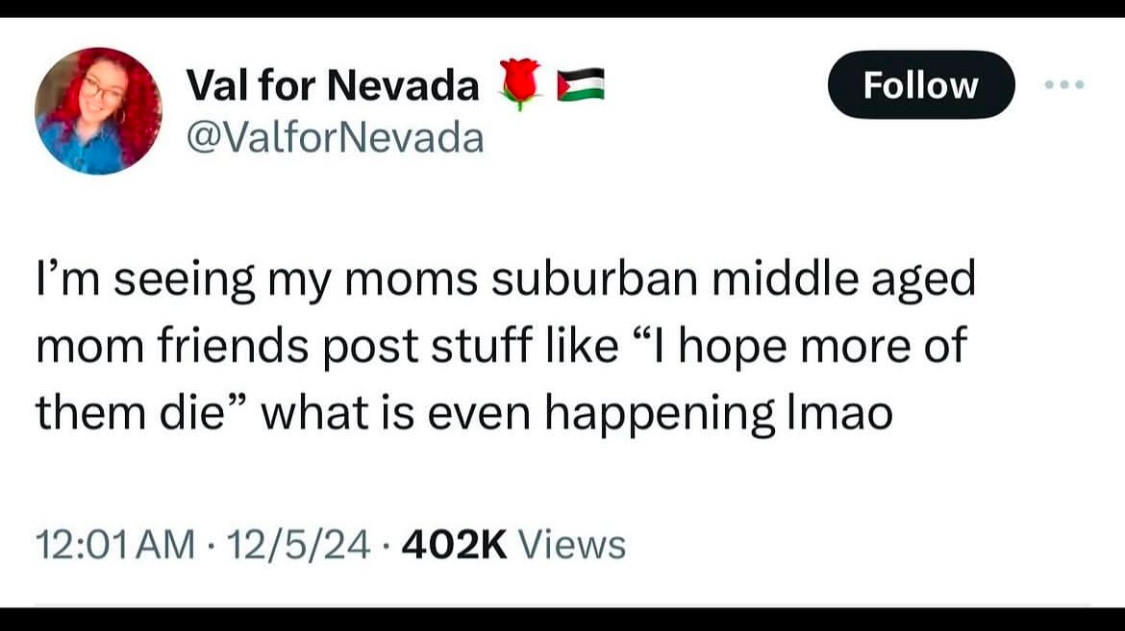
Post details
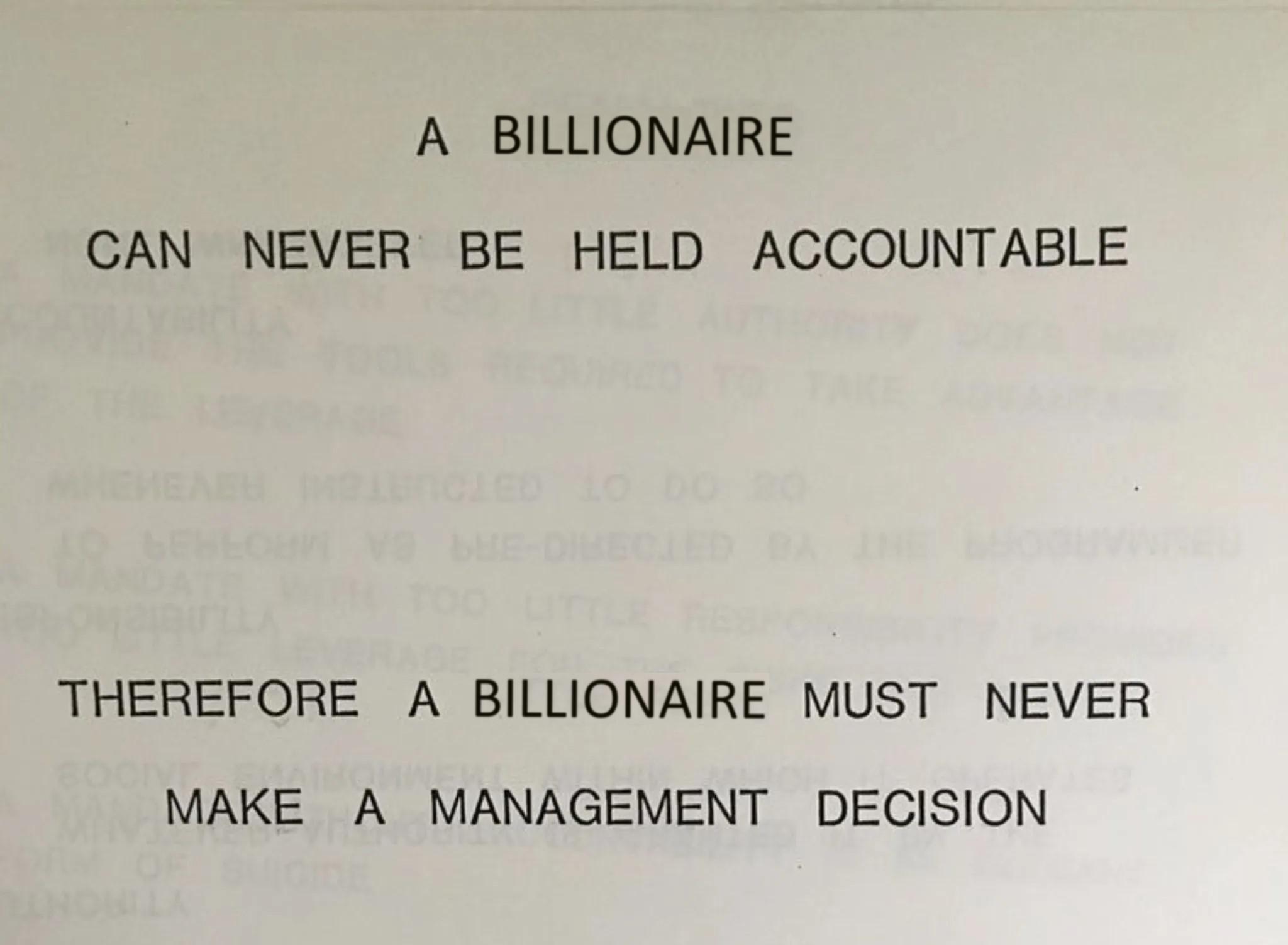
its so depressing that a man can't manage a system of precarity and excess mortality organized solely for shareholder wealth for 20 very profitable years without occasionally getting shot to death at 6:45am in midtown new york by a person dressed in a hooded jacket. what has become of this country?