Post details
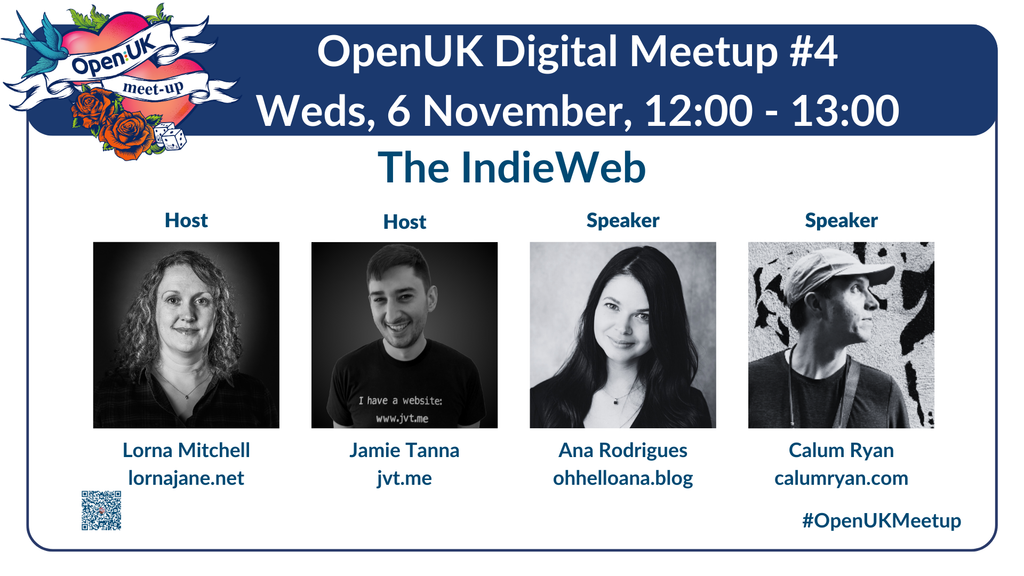
Attached: 1 image The Indie Web Ana Rodrigues https://ohhelloana.blog, Calum Ryan https://calumryan.com will join us with our hosts Lorna Mitchell https://lornajane.net and Jamie Tanna https://jvt.me for the fourth OpenUK Digital Meetup on November 6. Register now https://openuk.uk/event-calendar/digitalmeetup4 #opensource #opensourcesoftware #digitalmeetup